New technology is invisible to a user and identifies fraud accurately 95% of the time in trials

Information systems professors at BYU have created a technology using JavaScript that can detect online identity fraud simply by measuring interaction behaviors like keystroke speed.
The detection system, refined over four observational studies of more than 1,000 participants, was 95.5% effective at correctly determining “fraudulent activity” in experimental settings where subjects entered in both personal information (names, email, etc.) and information belonging to other people on online forms.
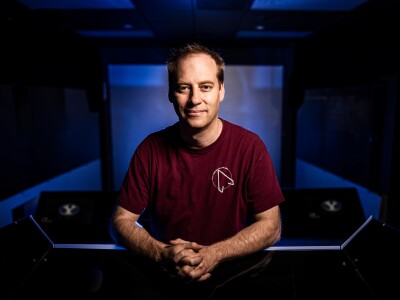
“When you watch how someone interacts with devices, you gain insight into mental processes,” said study co-author David Wilson, a BYU professor of information systems. “Our motor movements and our cognitive activities are very intimately linked — subconsciously in many cases.”
Wilson said when it comes to names and other familiar login information, humans naturally develop muscle memory that results in more fluid typing. He and his collaborators, including fellow BYU professor Jeffrey Jenkins, Joseph Valacich (University of Arizona) and David Kim (TCU), have based their technology on the idea that entering stolen identity credentials should take longer than typing one’s own information. “Typing should feel different when typing your own name versus typing a stolen name,” Wilson said.
According to their experimental studies, there is a significant difference — “very different behaviors, very different patterns of interaction,” Wilson said — when people enter their own information versus entering someone else’s in an identity fraud scenario.
Those “keystroke dynamics” form the basis for their identity fraud detection system. And while other fraud detection systems are widely available, Wilson and Jenkins said their new tech overcomes a significant weakness of existing systems: increased friction due to the introduction of verification steps that make potential clients less likely to finish an application.
“The reason why this is such a compelling technology — and such a compelling idea — is that what we are measuring can be captured seamlessly by any device that can run JavaScript,” Wilson said. “All of our capture technology is based on a script that’s running behind the scenes in a browser. JavaScript will keep track of timings and how things are being typed and then JavaScript reports that back to our servers. Because there is no effect on the user experience, this technology can be used across an entire web-based platform.”
Credit card companies, banks and other financial platforms that need to verify the identities of their users have a large incentive to catch fraud and not issue loans to people who don’t exist. They also don’t want to turn away potential customers with a clunky application process. Wilson said this technology provides a novel way to balance fraud defense and friction.
“It’s a low-friction way to flag, say, the 10% most suspicious-looking applications and then have that smaller population do a few high-friction things to verify their identity,” Wilson said. “And then you protect the customer experience for a majority of your customer base.”